In today’s rapidly evolving digital landscape, organisations face increasingly sophisticated cyber threats. The traditional perimeter-based security approach is no longer sufficient to protect valuable data and systems from sophisticated attacks. As a result, a paradigm shift towards a Zero Trust Security model has gained significant traction, particularly in cloud environments like Amazon Web Services or Microsoft Azure. Zero Trust Security adopts a proactive and comprehensive approach to secure data, regardless of its location, by assuming that no network or user can be trusted by default. This short article, inspired by the variety of presentations conducted at the 2022 AWS Re:Invent conference in Las Vegas and the 2023 AWS Summit in London, explores how Zero Trust Security principles can be implemented in Amazon Web Services.
Least Privilege Access: The foundation of Zero Trust Security lies in granting the principle of least privilege access. Instead of relying on traditional network-based segmentation, AWS implements granular access controls using Identity and Access Management (IAM). IAM enables organisations to define fine-grained permissions for AWS resources, limiting access to only those who require it. By enforcing least privilege access, the attack surface is significantly reduced, minimising the potential impact of compromised credentials or unauthorised access.
Multi-Factor Authentication (MFA): Implementing Multi-Factor Authentication adds an additional layer of security to the authentication process. AWS supports various MFA options, including hardware tokens, virtual MFA devices, and biometric authentication. By requiring multiple factors to authenticate users, even if passwords are compromised, unauthorised access can be prevented.
Zero Trust Security adopts a proactive and comprehensive approach to secure data, regardless of its location, by assuming that no network or user can be trusted by default
Network Segmentation: Zero Trust Security emphasises micro-segmentation to compartmentalise resources and limit lateral movement within the network. AWS offers Virtual Private Cloud (VPC), enabling organisations to create isolated network environments and apply strict network access controls. By deploying security groups and network ACLs, organisations can enforce granular inbound and outbound traffic rules, ensuring that only authorised communication occurs between resources.
Encryption and Key Management: Protecting data at rest and in transit is crucial in a Zero Trust Security model. AWS provides robust encryption capabilities through services such as AWS Key Management Service (KMS), which allows organisations to manage and control encryption keys. By encrypting sensitive data and managing keys effectively, organisations maintain control over their data, even if it is compromised.

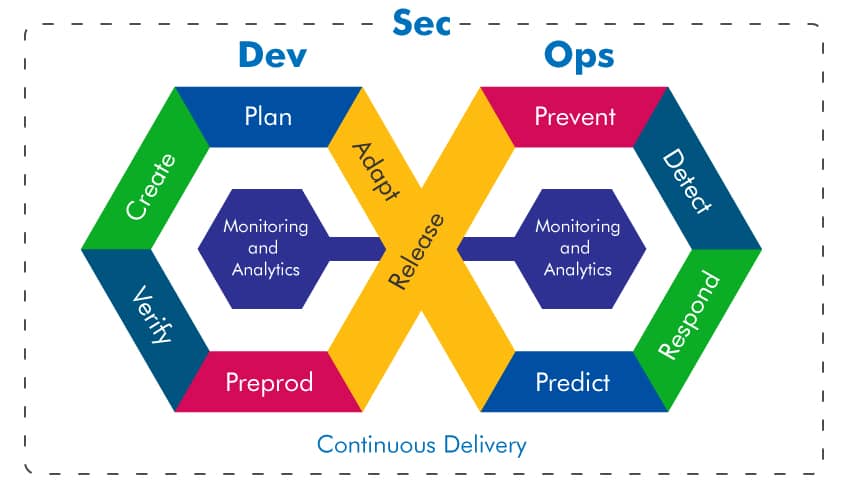
Continuous Monitoring and Logging: Zero Trust Security relies on continuous monitoring and logging to detect and respond to potential security incidents promptly. AWS provides services such as AWS CloudTrail, which enables organisations to monitor and log all API calls made within their AWS accounts. Additionally, services like AWS GuardDuty and AWS Security Hub provide threat detection and security insights, enhancing the ability to identify and respond to suspicious activities.
Automation and Orchestration: In a large and dynamic cloud environment, manual security processes can be challenging to scale and prone to errors. AWS offers services such as AWS Identity and Access Management Access Analyzer and AWS Config to automate security configuration assessments and enforce compliance policies. By automating security processes, organisations can ensure consistent and reliable enforcement of Zero Trust Security principles.
As cyber threats continue to evolve, a Zero Trust Security model becomes imperative to safeguard critical data and systems..
Security Analytics and Artificial Intelligence: AWS offers security analytics services such as Amazon GuardDuty and Amazon Macie, which leverage machine learning and AI to identify anomalous behaviour and protect against insider threats. These services continuously analyse vast amounts of data and provide actionable insights to enhance security posture.
AWS Verified Access: the service is based on the principles of Zero Trust and ensures that each application request undergoes validation prior to access authorisation. By eliminating the requirement for a VPN, Verified Access streamlines the remote connectivity process for users and minimises the administrative complexities faced by IT administrators.
Amazon VPC Lattice: An application networking service that establishes and safeguards communication channels between your services. It gives the flexibility to define policies for managing, accessing, and monitoring network traffic, simplifying and unifying connectivity across instances, containers, and serverless applications.
Amazon Verified Permissions: a scalable service for managing permissions and implementing precise authorisation within the applications you create. It leverages Cedar, an open-source policy language that is both expressive and analyzable. With this service, developers and administrators can establish policy-based access controls using roles and attributes, allowing for more detailed and context-aware management of access.
Implementing Zero Trust Security in AWS requires a comprehensive and layered approach. By combining strong access controls, network segmentation, encryption, continuous monitoring, automation, and intelligent analytics, organisations can establish a robust security framework that aligns with Zero Trust principles.
As cyber threats continue to evolve, a Zero Trust Security model becomes imperative to safeguard critical data and systems. AWS provides a wide range of services and features that enable organisations to embrace Zero Trust Security principles effectively. By adopting a proactive and comprehensive approach to security, organisations can fortify their defences, detect potential threats, and protect their valuable assets in the AWS.