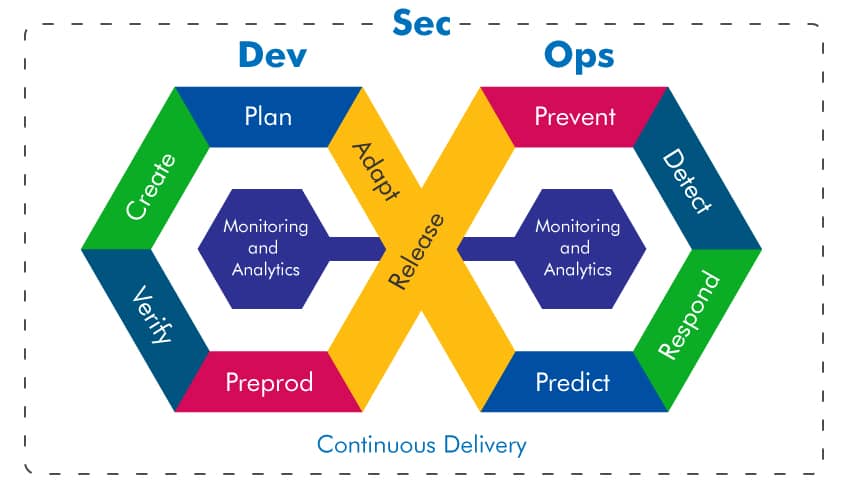
A recent industry report has revealed a troubling trend: nearly two-thirds of organisations have experienced cloud security incidents in the past year, but 𝗼𝗻𝗹𝘆 𝟵% 𝗱𝗲𝘁𝗲𝗰𝘁𝗲𝗱 𝘁𝗵𝗲𝗺 𝘄𝗶𝘁𝗵𝗶𝗻 𝘁𝗵𝗲 𝗳𝗶𝗿𝘀𝘁 𝗵𝗼𝘂𝗿.
On average, it takes over 24 hours to respond, giving attackers time to move laterally, escalate privileges, and cause real damage.
This isn’t just a security issue, 𝗶𝘁’𝘀 𝗮 𝗯𝘂𝘀𝗶𝗻𝗲𝘀𝘀 𝗿𝗶𝘀𝗸.

Long detection windows undermine customer trust, damage corporate reputations, endanger regulatory compliance, and impact operational resilience.
So what is causing this delay in detecting incidents? This delay is likely caused by a combination of factors, including 𝗮𝗹𝗲𝗿𝘁 𝗳𝗮𝘁𝗶𝗴𝘂𝗲, disconnected toolsets, and limited visibility across hybrid and multi-cloud environments.
As cloud adoption accelerates, so must our detection and response strategies. That means automated threat detection, better signal-to-noise ratios, and cloud-native security architectures that scale with speed and complexity.
We can’t defend what we can’t see, and we can’t wait 24 hours to act.