For today’s CIOs and CTOs, the cloud isn’t just a place to run apps, it’s the engine of digital transformation, fueling rapid innovation and scale.
But here’s the paradox: That very speed often clashes head-on with the imperative of robust security.
Achieving the right equilibrium, unleashing speed while maintaining control is the most critical challenge facing technology leadership.
Security shouldn’t be a roadblock. It must be an accelerator.

The Cloud Paradox: Where Speed Meets Risk
The tension at the core of cloud innovation stems from its native characteristics:
- Elasticity & Speed: Developers provision infrastructure in minutes. This is great for agility, but manual security oversight is slow and leads to misconfigurations, widely cited as a top cause of cloud breaches [e.g., IBM Cost of a Data Breach Report, SANS Institute, Palo Alto Networks Cloud Security Report].
- Shared Responsibility Trap: Your cloud provider secures the infrastructure of the cloud, but you are responsible for security in the cloud (data, access, applications, network configuration). Misunderstanding this is a common path to failure.
- Distributed Architecture: Microservices, serverless functions, and multi-cloud environments fragment the attack surface, making traditional perimeter security models obsolete and complicating control.
Four Strategies to Harmonise Security and Innovation
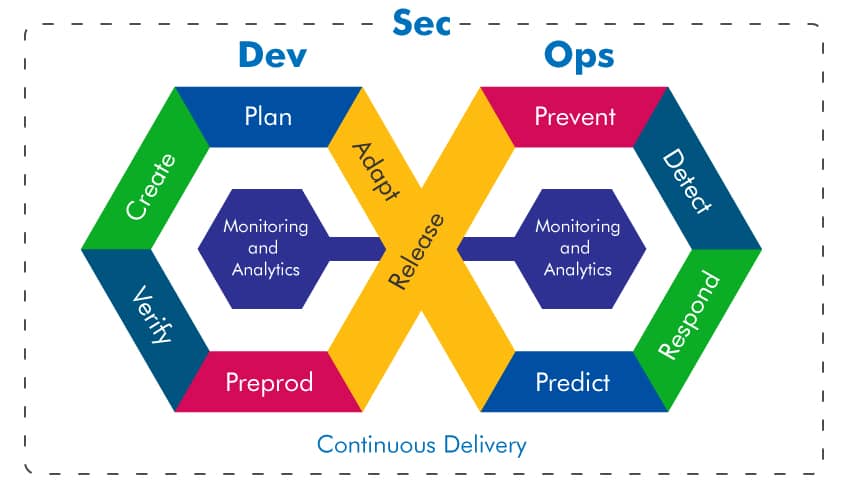
To resolve this paradox, tech leaders must embed security directly into the innovation lifecycle, moving from a slow “detect and respond” model to a proactive “predict and prevent” one.
1. Shift Left with DevSecOps
This is the most impactful move: Integrating security into the DevOps pipeline from the start.
- Automation is Key: Utilize Infrastructure as Code (IaC) tools (Terraform, CloudFormation) and integrate automated security testing (SAST, DAST, SCA) before deployment.
- Security Gates: Embed automated policy checks in your CI/CD pipelines. If a configuration violates a baseline security standard (e.g., an exposed S3 bucket), the pipeline fails automatically.
- Code Review & Templates: Empower developers by providing reusable security libraries and trusted reference architectures they can import and use, eliminating the need to build security from scratch.
2. Adopt a Unified Cloud Security Posture Management (CSPM)
When your environment spans multiple services and clouds, visibility is paramount.
- Centralised Visibility: Implement a CSPM solution to continuously monitor and report on security misconfigurations across all cloud accounts.
- Prioritise Remediation: Use CSPM to move beyond overwhelming vulnerability lists. Prioritise risks based on severity, exploitability, and business impact to focus effort where it matters most.
3. Implement Zero Trust Architecture (ZTA)
The traditional network perimeter is obsolete. Zero Trust treats every user, device, and application as a threat until verified.
- Never Trust, Always Verify: Enforce strict Identity and Access Management (IAM). Demand Multi-Factor Authentication (MFA) and strictly adhere to least privilege access principles for every account, human or service.
- Micro-segmentation: Break down the network into smaller, isolated zones. This confines any potential breach to a small area, preventing lateral movement and protecting critical assets.
4. Foster a Security Conscious Culture
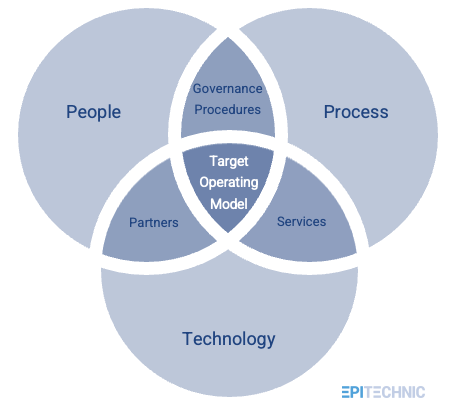
Technology and processes are only as strong as the people who manage them.
- Training & Empowerment: Give engineers regular, contextual security training. Empower them to be security champions within their own agile teams.
- Transparent Communication: Security teams must communicate risks clearly, focusing on collaboration rather than blame. When a vulnerability is found, the discussion should center on how to automate its prevention next time.
The Path Forward for Technology Leaders
The successful organisation in the cloud era is one where innovation and security are interdependent. Innovation provides the features; security provides the trust necessary to deploy them globally.
Your mandate as a CIO/CTO:
- Allocate Budget: Dedicate resources to automation tools and cloud native security talent.
- Define Metrics: Measure the time to market for a SECURE release, not just the number of vulnerabilities found. Security must be measured as an enabler.
- Lead by Example: Demonstrate that security policies are essential safeguards, not just bureaucratic hurdles.
By treating security as code and making it an integral part of the development workflow, you move faster, deploy smarter, and build the resilient digital future your customers expect.